A significant data breach potentially compromising over 93,000 Indonesian consumer SMS records has come to light, sending ripples of concern across the digital landscape. The exposed data, highly sensitive in nature, reportedly includes One-Time Passwords (OTPs), verification codes, telecommunication operator metadata, timestamps, mobile phone numbers, and application-specific codes originating from a multitude of popular platforms such as Shopee, TikTok, Samsung, LAZADA, and AirAsia. The ramifications of such a breach are far-reaching, impacting individual security, corporate reputation, and the overall digital trust ecosystem.
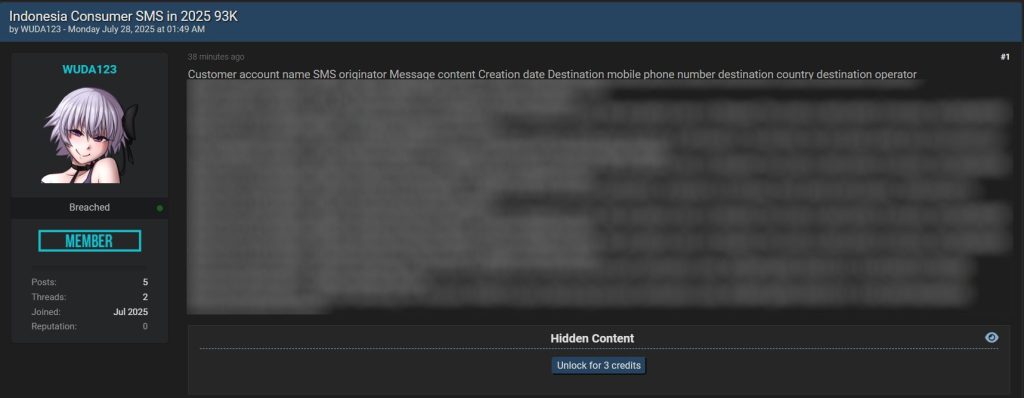
The initial discovery of this potential threat was attributed to Dark Web Informer, a reputable source of cyber threat intelligence, with the information disseminated via the platform X (formerly Twitter). The alleged perpetrator behind this data exposure goes by the alias WUDA123, whose activities were detected within the BreachForums, a known hub for cybercriminal activity and a marketplace for illicit data. The BreachForums is a notorious online platform where hackers and cybercriminals congregate to share, trade, and sell stolen data, exploits, and hacking tools. Its existence underscores the persistent threat landscape and the ease with which malicious actors can connect and operate in the digital underground.
The unauthorized disclosure of this data presents substantial risks to the affected individuals. OTPs and verification codes, designed as a crucial security layer for authentication, now lie in potentially malicious hands. This exposure can be exploited to gain unauthorized access to personal accounts, perpetrate fraudulent financial transactions, or facilitate identity theft. Moreover, the compromised telecommunication operator metadata, timestamps, and mobile phone numbers could be leveraged to track user locations, monitor activities, and orchestrate highly targeted phishing campaigns. Phishing attacks, in particular, can be crafted with alarming precision using this information, increasing the likelihood of successful deception and data compromise.
The scope of the data breach extends across various sectors, potentially affecting e-commerce platforms like Shopee and LAZADA, social media giants like TikTok, electronics manufacturers such as Samsung, and travel services like AirAsia. Users of these platforms should exercise extreme vigilance regarding phishing attempts and any suspicious activity detected within their accounts. Telecommunication operators also face scrutiny and are urged to bolster their security measures to prevent similar data leaks from occurring in the future. This includes implementing robust data encryption, access controls, and regular security audits to identify and address vulnerabilities.
It is essential to emphasize that the information regarding this breach originates from cyber threat intelligence sources and forums known for attracting cybercriminals. While the authenticity of the data leak has not been independently verified, the scale and sensitivity of the information involved demand serious and immediate attention. Law enforcement agencies and cybersecurity experts are likely investigating the claims to determine the full extent of the breach and identify the responsible parties.
Recommended Actions
In light of this potential data breach, individuals and organizations must take proactive steps to mitigate the risks:
-
Password Modification: Immediately change passwords for all accounts that may be affected, with particular attention to those associated with applications and platforms mentioned in the reported data leak. Employ strong, unique passwords for each account, avoiding easily guessable information or reusing passwords across multiple platforms. A strong password should consist of a combination of uppercase and lowercase letters, numbers, and symbols, and should be at least 12 characters long.
-
Two-Factor Authentication (2FA) Activation: Enable 2FA on all accounts that offer this security feature. Two-factor authentication provides an additional layer of security beyond a password, typically requiring a code generated by a mobile app or sent via SMS to verify the user’s identity. This makes it significantly more difficult for attackers to gain unauthorized access, even if they have obtained the user’s password.
-
Phishing Awareness: Remain highly vigilant and skeptical of unsolicited emails, text messages, and phone calls requesting personal information. Never click on links or download attachments from unknown or untrusted sources. Verify the legitimacy of any communication before providing sensitive information. Phishing attacks often mimic legitimate communications from trusted organizations, so it is crucial to scrutinize the sender’s address, the content of the message, and any links or attachments.
-
Credit Report Monitoring: Regularly monitor your credit reports for any unauthorized activity. Report any suspicious activity to your financial institutions and credit reporting agencies immediately. Credit reports provide a detailed history of your credit activity, including new accounts, loans, and credit inquiries. Monitoring your credit report can help you detect identity theft and other fraudulent activity early on.
-
Incident Reporting: If you believe your personal information has been compromised, report the incident to the appropriate authorities, such as the Badan Siber dan Sandi Negara (BSSN) – the National Cyber and Crypto Agency of Indonesia – or your local law enforcement agency. Reporting the incident can help authorities investigate the breach and take steps to prevent further harm.
Wider Implications
This alleged data breach highlights the escalating threat of cybercrime in Indonesia and the pressing need for stronger cybersecurity measures. Organizations of all sizes must prioritize investments in cybersecurity best practices, including regular vulnerability assessments, security awareness training for employees, and the implementation of strict access controls. These measures are essential to protect sensitive data and prevent cyberattacks.
The government also plays a crucial role in safeguarding the personal data of its citizens. This includes enacting robust data protection laws, enforcing compliance with cybersecurity standards, and collaborating with international organizations to combat transnational cybercrime. Strong data protection laws provide a legal framework for protecting personal data and holding organizations accountable for data breaches. Enforcement of cybersecurity standards ensures that organizations are implementing appropriate security measures to protect data.
Furthermore, it is essential to raise public awareness about the risks of cybercrime and how to protect oneself from these threats. This can be achieved through public education campaigns, training workshops, and other initiatives. Educating the public about cybersecurity best practices can empower individuals to take proactive steps to protect themselves from cyber threats.